emCrypt
The cryptographic library for secure applications
emCrypt is a secure and efficient implementation of essential cryptographic algorithms specifically designed for embedded systems.
Overview
Designed with both efficiency and security in mind, emCrypt serves as a reliable encryption toolkit, offering all of the key components needed for today's secure protocols. In a world full of connected devices, keeping data secure is crucial. With emCrypt, users can trust that their embedded devices are protected against potential threats.
Key features
emCrypt includes various features designed to meet modern security needs, providing high-performance cryptographic solutions with a focus on clean and secure code.
Modern cryptogrphay standards
emCrypt adheres to the latest cryptographic standards, ensuring that it provides robust and up-to-date security mechanisms suitable for protecting sensitive data against threats.
Secure, fast, and clean code
The library is designed with a focus on security, performance, and efficiency. The encryption solutions are robust, reliable, and written in code that is clean and easy to maintain.
Intuitive API
emCrypt includes comprehensive support for advanced cryptographic operations such as key derivation, key wrapping, and key encapsulation.
Use cases
emCrypt offers versatile solutions for securing data in various scenarios. Whether safeguarding data during transmission with robust encryption protocols such as emSSL and emSSH, protecting sensitive information stored on devices using XTS-AES encryption, or ensuring data integrity through digital signatures, emCrypt provides comprehensive security against unauthorized access and data tampering.
Securing data in transmission
emCrypt ensures the protection of data during transmission through robust encryption protocols. Our solutions, such as emSSL and emSSH, use emCrypt's powerful encryption algorithms to secure communications over the internet, preventing unauthorized access and data breaches.

Securing data at rest
emCrypt provides robust encryption for data stored on devices, safeguarding sensitive information from unauthorized access. With our XTS-AES encryption technology, we ensure that data remains protected even if the physical device is compromised. This is essential for securing personal data, financial records, and confidential business information.

Ensuring data integrity
emCrypt uses digital signatures to verify that data comes from a trusted source and has not been tampered with. Using advanced cryptographic algorithms such as RSA, ECDSA, and EdDSA, emCrypt enables the creation and verification of digital signatures. This ensures that data remains tamper-free and authentic.
How emCrypt works


emCrypt offers a wide range of cryptographic capabilities which are the basis of many security protocols. It can be configured for the minimal memory footprint of constrained devices but can also scale to faster performance on systems that have more resources. A high-quality product, it is designed to be used with ease and without limitations. emCrypt has proven itself within SEGGER and is the foundation that emSSL, emSSH and emSecure-RSA, emSecure-ECDSA are built upon.
emCrypt offers several advanced features, including
- An extensive 2,000-page manual that covers all API features and functions
- Decoupled implementation ensures that only the necessary components are linked
- Public key cryptography with RSA, DSA, ECDSA, and EdDSA
- Fast, tunable ciphers, hash algorithms, and message authentication codes (MACs)
- Random bit generation and cryptographically secure pseudo-random numbers
Written in ANSI C, it is compiler- and target-independent. It can be implemented in PC applications and embedded systems.
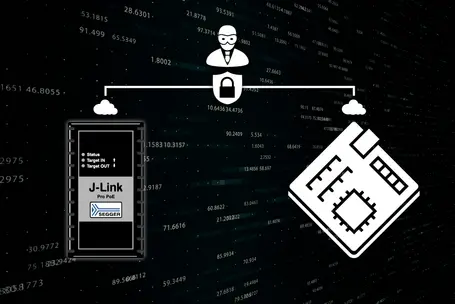
End-to-end encryption
emCrypt provides a range of algorithms, functions, and cryptographic tools needed to implement different security schemes and protocols. It supports advanced protocols like emSSL (SSL and TLS) and emSSH, both of which are built on emCrypt.
For a deeper understanding of how to use emCrypt, explore our example applications. These examples demonstrate how to establish secure communication with end-to-end encryption and set up end-to-end encrypted communication between two clients without user interaction on a single, potentially insecure channel using ECDHE Key Agreement.
In use at SEGGER
emCrypt has proven itself within SEGGER and is the foundation of several security-related tools such as emSSL, emSSH, emSecure-RSA, and emSecure-ECDSA. All of these tools can be combined or used separately.
Purchase information
emCrypt is only available upon request. Users receive emCrypt as source code, which provides transparency for all included modules and allows inspection by auditors. Written in ANSI C, it is compiler and target independent. It can be implemented in PC applications and embedded systems. Sample applications with source code are also available to demonstrate how to use the emCrypt API.
Free from an open-source or required-attribution license, emCrypt can be integrated into any free, commercial or proprietary product without the need to disclose the combined source.
Pluggable cryptographic algorithms and hardware acceleration are supported by emCrypt. As an option, hardware acceleration for popular microcontrollers such as Kinetis CAU, STM32 CRYP, EFM32 CRYPTO, LPC18S and LPC43S is available.
| Package contents | |
|---|---|
| emCrypt |
|

Licensing
The software is available under various embedded software license models and can be delivered as source code. All commercial licenses are based on a one-time payment, are royalty-free, and include six months of updates and support from SEGGER’s Embedded Experts.
There are no subscription fees, ensuring predictable and fixed costs over the entire product lifetime.
For non-commercial use, evaluation, and educational purposes, the software is provided under SEGGER’s Friendly License.
Get in touch with us
Have questions or need assistance? Our Embedded Experts are here to help!
Reach out to us for:
- Licensing quotes
- Technical inquiries
- Project support