Secure Product Lifecycle Management
With the rise in the number of devices that are always online, security requirements have also risen significantly.
Addressing the security of these devices has become imperative and requires a flexible lifecycle management, that allows field updates at any time in the field.
- Develop secure authenticated firmware for embedded systems
- Authenticate the hardware in production
- Provide secure maintenance updates in the field
Security for your Embedded Applications
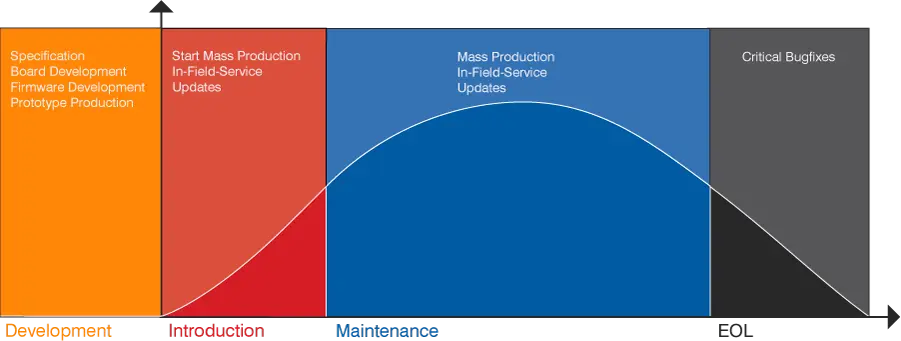
Due to the increasingly open networking of electronic devices, the demand for security solutions for embedded systems is also increasing. Any device should be fortified in a way, that its firmware is safe and cannot be attacked or modified. Especially in safety-critical segments, such as medical, industry and automotive, the demand for security concepts to prevent cyber attacks is growing. One of the key mechanisms recommended by security experts are secure firmware update mechanisms. The figure below gives an overview of the three stages required to build a secure product lifecycle management process, that includes firmware updates in the field. Updates can be applied over the air (FOTA/OTA) or by service technicians or the customers themselves.
Three Stages of Secure Product Lifecycle Management
Secure Product Lifecycle Management means, that at any stage of a product's life, it can be maintained and updated to adapt to changing environments, whether the changes are beneficial or hazardous.
SEGGER's offer on Secure Product Lifecycle Management will be applied in the following three stages:
- Develop & Plan Secured Firmware
- Authentication in Production
- Secure & Efficient In-Field Firmware Updates
1. Develop & Plan Secured Firmware
A modern device has to withstand a multitude of threats. These include attacks on the intellectual property and abusing the device. To protect a device from such threats, it needs to be equipped with a multitude of security layers adding to the resource requirements of the system.
In microcontroller-based systems, resources are limited, so these tools need to be tailored for the use in such systems. SEGGER's tools and libraries are known for their economical use of resources. A key security component is a method to update the firmware or even the boot loader.
SEGGER offers emLoad, a proven bootloader that minimizes the resource requirements of the firmware update and provides the necessary security and authentication using the SEGGER encryption library emCrypt to safely update a device in the field.
2. Authentication in Production
It is common to employ a contract manufacturer (CM) for mass production. CMs have access to customer IP and large quantities of the components they are contracted to assemble. Because of this, it is essential that customers control both, their IP and limit CM production, in order to prevent theft and to secure revenue.
This is the domain of Flasher SECURE and emSecure, which enable secure authentication even in environments that are not under full control of the IP owner. With this tool set the IP owner regains full end-to-end control of their production process.
3. Secure & Efficient In-Field Firmware Updates
The tools mentioned before represent the cornerstones of Secure Product Lifecycle Management. Being able to counter new threats by updating devices in the field has proven to be vital in many applications already.
SEGGER provides developers with all tools required to deploy a secure management system for embedded devices. Whether the updates are executed over the air (emLoad) or by service technicians (Flasher Portable Plus), SEGGER can offer a solution for all your requirements.
Software and Development Tools for Your Secure Product Lifecycle
SEGGER provides an RTOS plus communication and security software, so developers get a head start, benefiting from SEGGER's decades of experience in the industry. SEGGER's professional software libraries and tools for Embedded System development are designed for simple usage and are optimized for the requirements imposed by resource-constrained embedded systems.
The company also supports the entire development process, with affordable, high quality, flexible, easy-to-use tools, and middleware components.
The J-Link debug probes, with Ozone the accompanying debugger and performance analyzer, and Embedded Studio the powerful cross platform C/C++ IDE, are available to support developers in creating their own embedded systems.
Please contact our sales team to receive a demonstration of a secure product lifecycle implementation.