emSecure - Signed Downloads
SEGGER provides digital signatures for all files that are available for download in SEGGER's Download area.
All SEGGER downloads have been signed with SEGGER's emSecure Sign & Verify!
Signed downloads are a must-have to provide more security to users. Modifications of data during sending - be it through a virus, a trojan or any willful manipulation - will no longer go unnoticed. SEGGER's emSecure Sign & Verify can make sure that data stored to and recalled from a server is unchanged.
What is the digital signature of the file?
The digital signature is generated with a private key by SEGGER. It is intended to assure that the software comes from SEGGER and has not been modified by anyone. Even in case the SEGGER webpage would be hacked, the attacker could not generate valid signatures for files.
How can downloads be verified?
Your downloaded files can be verified in a few steps:
- Get a free copy of emSecure Sign & Verify tool which comes with SEGGER's public key to verify SEGGER downloads.
- Get the signature file "*.sig" which is provided next to each download button at https://www.segger.com/downloads/.
- Place the signature file into the same directory as your download.
- Once you have downloaded a file and the appropriate signature to your PC, drag the download or the signature file onto Sign & Verify.
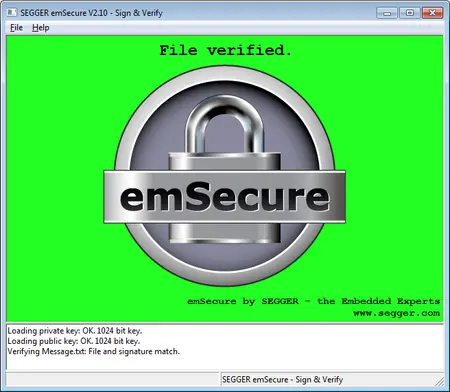
Sign & Verify will try to verify the file by its signature with the public key files residing in the Sign & Verify directory. The green flashing window, as shown in the screenshot, will show that the downloaded file is authentic and has not been modified. If the file or the signature would have been modified, either on the web server, while downloading it, or on the local computer, Sign & Verify would not be able to verify the file and flashes red.
To be sure that Sign & Verify and SEGGER's public key have not been modified and that you get a genuine version, you may also contact info@segger.com and request to get Sign & Verify via e-mail.
How are the signatures generated?
The signatures are generated at SEGGER by a server running in the local network. This server is a "deeply embedded system", a microcontroller running SEGGER's software: embOS, emNet and emSecure. The private keys are stored inside the microcontroller and can not be read out.
This is a big difference to traditional hashes, such as MD5. Here an attacker who would compromise the website, gaining the ability to exchange file for download, could present them with a valid MD5 checksum as well.
Unlike Windows or Linux systems, the microcontroller running SEGGER software does not have vulnerabilities that allow attacking and compromising the server, which means the keys are safe. There is no copy of the private keys anywhere in the SEGGER network, only a paper copy of the keys exist in a safe, so even in the unlikely case of the company's network becoming compromised, the keys would still be safe.