Authorized Flashing Security Feature
Authorized Flashing limits the number of flash programming cycles and protects the Flasher against non-authorized access in the case of external production.
Overview
With the help of the "Authorized Flashing" feature, a maximum number of programming cycles can be set (in CntDown.txt) while the Flasher is configured for production, thereby limiting the number of devices that can be programmed. Companies which have contracted out production can thus protect themselves against a third party producing more than the targeted number of devices and possible counterfeiting. In the production facility there is no way to change the Flasher configuration.
Current Flashers support the creation of what is called a secure area which allows for pre-configuring the Flasher with a given setup which can be then shipped to the external production facility while preventing any read out of the Flasher contents via file access mode, FILE I/O functionality (J-Link Commander) or RS232 commands.
Once the pre-defined number of devices is programmed, the Flasher must be re-programmed to start a new programming cycle. This has to be carried out by the owner of the Intellectual Property directly on the Flasher.
Creating the Secure Area
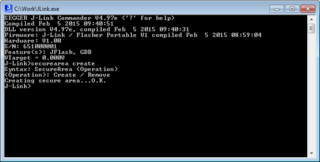
By default, Flashers are shipped with a public area only (full Flasher flash size accessible via file access mode etc.). The secure area has to be activated/created once, to make use of it. This will reserve half of the Flasher storage size for the secure area, i.e. around 64 MB for current models. The secure area can be removed at any time, thus releasing the full flasher storage to the public area again. The secure area can be created or removed via J-Link Commander, which is part of the software package that comes with the Flasher.
The following secure area related commands are available in J-Link Commander:
- securearea create
- securearea remove
When creating or removing the secure area, all configuration and data files currently stored on the Flasher are lost. This should be noted before adding or removing the security area.
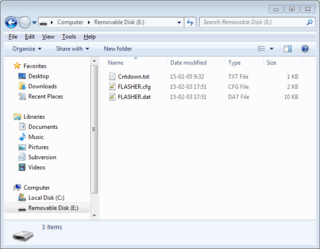
Moving Files to the Secure Area
Before moving configuration + data to the secure area, proper functionality of the setup should be verified in normal stand-alone mode. Once the setup is working as expected, do the following, to move the configuration + data into the secure area:
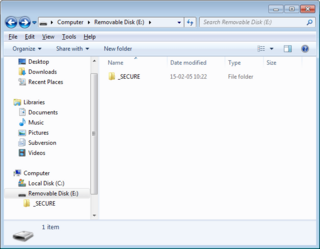
- Reboot the Flasher (This time do not enter file access mode, otherwise, contents will not be moved to the secure area). Depending on the configuration and data file size, it may take a while before the Flasher Power LED (Green) illuminates. Once it turns on, this means all contents have been moved to the secure area and the _SECURE folder in the public area has been deleted.
- Now the Flasher can be used in stand-alone mode, as normal, but the files cannot be read back by the user/operator.
Considerations to Be Taken When Using the Secure Area
When using the secure area, some things need to be considered:
- All features like multiple file support, patch file support etc. can also be used when operating from the secure area.
- The secure area cannot be read back by any utility. Only the FLASHER.LOG is viewable and updated in the public area, even when Flasher operates from the secure area.
- If there are any files or folders in the public area (with the exception of the FLASHER.LOG) and there is also configuration/data present in the secure area, stand-alone flashing will fail because it is not clear which configuration/data should be used. In such failing cases, Flashers with Ethernet / RS232 interface will output an appropriate error message on programming. All Flasher models will output an appropriate error message in the FLASHER.LOG.
- Moving files from the public area into the secure area can be done multiple times. Each time files are moved from the public area to the secure area, all contents of the secure area are completely erased before the new files are copied over.